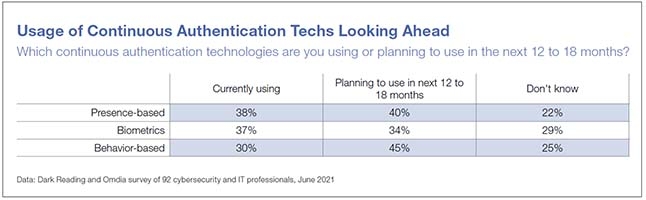
Security leaders are interested in continuous authentication technologies, especially behavioral-based capabilities.
A deep-dive study on the inner workings of incident response teams leads to a framework to apply...
Zero trust aims to replace implicit trust with explicit, continuously adaptive trust across users, devices, networks, applications,...
Remote Desktop aims to solve vulnerability issues with RDP by implementing robust access and security controls.
Deal will merge Bitglass’s security service edge technology with Forcepoint’s SASE architecture.
Graph databases can play a role in threat intelligence and unraveling sprawling data.
Startup created by former leaders of Microsoft Cloud Security Group experiencing rapid growth.
By demonstrating the following behaviors, security teams can more effectively move their initiatives forward.
Cybersecurity budgets are set to increase in 2022, but companies worry that complex IT networks and data...
De multiples vulnérabilités ont été découvertes dans les produits Adobe. Elles permettent à un attaquant de provoquer...